NO SERVERS • TOR • OFFLINE
Messaging built for hostile conditions.
Anonomi Messenger is an open source decentralized communication tool designed for high-threat environments. It works online over Tor, or completely offline over Wi-Fi, Bluetooth, and external storage.
Android-only. Built to reduce metadata exposure — not to promise magic anonymity.
The ultimate privacy tool
Anonomi Messenger is built around three pillars: communication, offline capabilities, and privacy & safety tools.
Communication
Messaging, groups, voice, walkie-talkie, and decentralized blogs.
Privacy & Safety
Payments, voice distortion, panic button, and stealth mode.
Offline & Network
Transports, offline maps, app distribution, and Postbox.
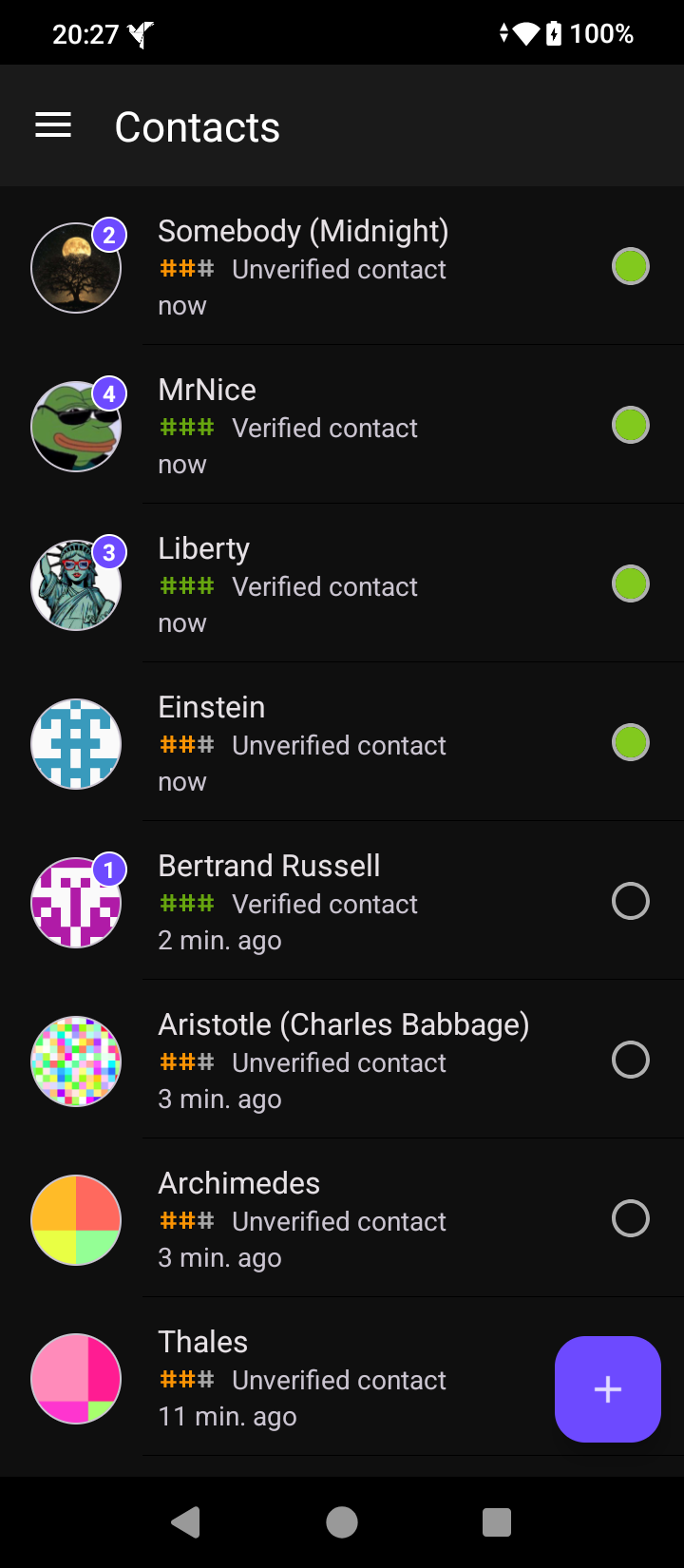
Communication
Messaging
Encrypted, decentralized messaging designed for hostile networks — online over Tor or fully offline over local transports. No central infrastructure to seize, log, or subpoena.
No central infrastructure to seize, log, or subpoena.
Route communication through Tor, with bridges when blocked.
Wi-Fi, Bluetooth, and external storage support when the network is the threat.
Text, images, voice, and location sharing in every conversation.
Groups & Open Groups
Create private groups for trusted circles or open groups (forums) for broader communities. Both support full media — text, images, voice, and location sharing.
Invite-only groups for trusted contacts. All messages are encrypted and synced peer-to-peer.
Public discussion spaces that anyone with an invitation link can join. Threaded conversations for organized discussion.
Text, images, voice messages, and location sharing work in both private groups and forums.
Reply to specific messages in group conversations to keep discussions organized and easy to follow.
Voice Messages
Record and send voice messages in any conversation. Voice data is encrypted and transmitted through the same peer-to-peer network as text and images.
Hold the microphone button to record, release to review or send. Works in private chats and groups.
Voice data is encrypted end-to-end and routed through the same peer-to-peer network as all other messages.
Send voice messages in private chats, groups, and forums — over Tor or any offline transport.
Play voice messages directly in the conversation without leaving the chat or opening a separate player.
Walkie-Talkie
Push-to-talk voice messaging via the volume button. Hold to record, release to send. Incoming messages auto-play for hands-free communication in the field.
Press and hold the volume button to record. Release to send instantly — no need to touch the screen.
Incoming walkie-talkie messages play automatically through the speaker for true hands-free operation.
Select a contact and use the volume button to send instant voice bursts — simple, focused, and distraction-free.
All walkie-talkie audio is end-to-end encrypted and routed through the same secure network as regular messages.
Blogs
Publish and follow blogs without servers or platforms. Posts sync peer-to-peer through the same decentralized network used for messaging.
Write blog posts with text, images, and offline map locations.
Interact with posts from people you follow — reactions and comments sync peer-to-peer.
Share posts from others to your own blog, amplifying content across the network.
A unified feed of posts from all blogs you follow, with individual blog views available.
Import RSS feeds from URLs or files and follow external content alongside peer blogs.
Invite contacts to follow your blog or share your blog status for discovery.
Privacy & Safety
Distorted Voice
Optional dynamic voice distortion applied to voice messages to reduce identification risk. Distortion is applied at recording time, so the original voice never leaves the device.
Distortion is applied before the audio leaves your device. The original voice is never transmitted or stored.
Voice characteristics are altered dynamically to prevent voiceprint identification while keeping speech intelligible.
Enable or disable distortion for each voice message. Choose when anonymity matters and when clarity is more important.
Voice distortion can be applied to walkie-talkie messages too — protecting your identity in real-time communication.
Panic Button
A last-resort mechanism triggered by a custom volume button sequence that you define. The trigger works across all screens — including the stealth calculator — with no need to navigate the app.
Define a personal sequence of short and long volume presses. Only you know the pattern.
Choose what happens when triggered: sign out, delete your account, or show a choice dialog at the moment of activation.
Designate trusted contacts who automatically receive a panic alert when the sequence is triggered.
The panic sequence can be triggered from the calculator disguise screen — no need to unlock the real interface first.
Stealth Mode
Hide Anonomi behind a calculator. When stealth mode is enabled, the app disguises itself as a functional calculator. A hidden interaction unlocks the real interface.
The app icon, name, and interface are replaced with a fully functional calculator that works normally.
A secret interaction within the calculator reveals the real Anonomi interface. Only you know the unlock method.
Anonomi doesn’t appear in recent apps, notifications, or system logs while stealth mode is active.
The calculator disguise persists across reboots and app updates — no need to re-enable it each time.
Private Payments
Monero payment requests designed to avoid leaking wallet metadata through unsafe channels.
Request a payment inside the conversation.
Generate a dedicated subaddress per request to avoid persistent identifiers.
Send a QR with subaddress + amount + description for scanning in a wallet app.
Avoid sharing payment details through insecure channels.
Offline & Network
Transports
Choose the best path for the situation: Tor when the internet is usable, local links when the internet is the threat.
Secure and anonymized routing over the internet. Bridges when Tor is blocked.
Communicate inside a local network with no traffic leaving the area.
Proximity comms for situations without internet or Wi-Fi infrastructure.
Store-and-forward via SD card or file transfer for checkpoints and border crossings.
Offline Maps & Location Sharing
Share locations without contacting external map servers. Import tile packs for offline navigation.
Designed to avoid third-party map providers.
Import trusted tile packs for fully offline usage.
Send coordinates to contacts without server round-trips.
Tile packs can be shared via trusted sources (onion/community mirrors).
Generate offline tile packs locally in your browser. Tile sources are only contacted after explicit user selection.
Offline Distribution
Install without app stores. Anonomi can be shared directly between Android devices using local connections, even when the internet is unavailable, monitored, or unsafe.
Share the app directly between Android devices over local connections — no internet or app store required.
A built-in offline kit bundles Anonomi and companion apps for distribution in disconnected environments.
The entire sharing process works over local connections — Wi-Fi, Bluetooth, or removable storage.
Shared app files include checksums so recipients can verify the app hasn’t been tampered with during transfer.
Anonomi Postbox
Receive messages while your main device is offline. Anonomi Postbox is a companion app installed on a separate Android device. It stays online and collects encrypted messages on your behalf, then delivers them automatically when your main device reconnects.
Messages arrive at the Postbox while you are offline and are delivered when your main device comes back online.
The Postbox cannot read your messages. It only stores and forwards encrypted data.
Link a Postbox to your account by scanning a QR code. No accounts, servers, or cloud services involved.
Anonomi works without a Postbox. Use it only if asynchronous delivery fits your threat model.
Threat model (pragmatic)
Anonomi assumes that in serious cases: network traffic is monitored and contacts may eventually be compromised.
- • Traffic from/to the device may be monitored.
- • Blocking and manipulation may occur.
- • Contacts may be compromised over time.
- • Physical inspection is a realistic risk.
- • Avoid centralized servers that can be seized or subpoenaed.
- • Provide offline options when networks are unsafe.
- • Reduce metadata leakage in everyday workflows.
- • Offer safety tools for coercive scenarios.
Download Anonomi Messenger
Anonomi is currently available for Android. Distribution is intentionally conservative: releases are signed, verifiable, and designed to be shared even without access to app stores.
The main app. Decentralized messaging over Tor or offline transports, with private payments, offline maps, and safety tools built in.
Latest version
Companion app for asynchronous message delivery. Install on a separate device to receive messages while your main phone is offline.
Latest version
Releases are signed and published with checksums. In high-risk environments, always verify before installing.
No Google Play, no trackers, no silent updates. Anonomi is distributed outside centralized app stores by design.
Anonomi is Android-only. iOS imposes architectural and policy constraints that prevent providing the level of privacy, network control, and offline operation required by Anonomi’s threat model. Supporting iOS would mean compromising on guarantees this project is not willing to weaken.